Table of Contents >> Show >> Hide
- What Is WebRTC, and Why Do People Disable It?
- Before You Disable WebRTC, Know What Will Break
- How to Disable WebRTC in Firefox in 2025
- How to Disable WebRTC in Chrome in 2025
- How to Disable WebRTC in Opera in 2025
- How to Test for a WebRTC Leak
- Should You Fully Disable WebRTC or Just Limit It?
- Real-World Experience: What It Actually Feels Like to Disable WebRTC in 2025
- Final Verdict
- SEO Tags
If browser privacy had a supervillain origin story, WebRTC would at least get a supporting role. It is incredibly useful, powering browser-based voice calls, video chats, screen sharing, and peer-to-peer connections without begging you to install a random plug-in from 2012. Very modern. Very convenient. Also, occasionally a little too chatty about your IP address.
That is why so many privacy-minded users still search for ways to disable WebRTC in 2025. Some want to reduce the risk of WebRTC leaks while using a VPN. Others simply do not use browser calling features and would rather shut the whole thing down than leave another door cracked open. The catch is that modern browsers no longer handle WebRTC the same way. Firefox still gives you a fairly direct route. Chrome and Opera? They are more like, “We heard your privacy concern, and in return we offer several side quests.”
This guide breaks down what WebRTC does, why people disable it, and the most realistic ways to turn it off or lock it down in Chrome, Firefox, and Opera in 2025. It also explains what will stop working, how to test for leaks, and when using stronger permissions plus a reputable VPN is smarter than going full scorched-earth mode.
What Is WebRTC, and Why Do People Disable It?
WebRTC stands for Web Real-Time Communication. In plain English, it helps browsers handle real-time audio, video, and data sharing. If you have ever joined a browser-based video call, shared your screen in a web app, or used a web messenger with voice chat, chances are WebRTC was quietly doing the heavy lifting.
So why disable something that useful? Because WebRTC can also reveal network details, including IP information, during the connection process. That matters most when you are using a VPN and expect your real IP address to stay tucked away like a secret family lasagna recipe. If a browser leaks that IP through WebRTC, your privacy setup starts looking less “fortress” and more “screen door on a submarine.”
People usually disable WebRTC for three reasons:
- They want to reduce the chance of a WebRTC leak exposing their real IP address.
- They do not use browser calling tools and would rather remove the feature entirely.
- They are tightening browser privacy settings as part of a larger setup that includes a VPN, stricter permissions, and tracker blocking.
Before You Disable WebRTC, Know What Will Break
This is the part many older tutorials glide past with the confidence of a magician who has already hidden the rabbit. Disabling WebRTC can break legitimate features, including:
- Google Meet and browser-based Zoom alternatives
- Discord in the browser
- Slack huddles or web calls
- Web-based screen sharing tools
- Some online classrooms, support chat systems, and telehealth portals
In other words, if you disable WebRTC, do not act shocked when your browser suddenly behaves like it has never heard of a microphone. For many users, the smarter move is not a total shutdown but a combination of tight camera and microphone permissions, a VPN with leak protection, and a quick leak test every so often.
How to Disable WebRTC in Firefox in 2025
If you want the most straightforward answer in this whole article, here it is: Firefox is still the easiest mainstream browser for disabling WebRTC.
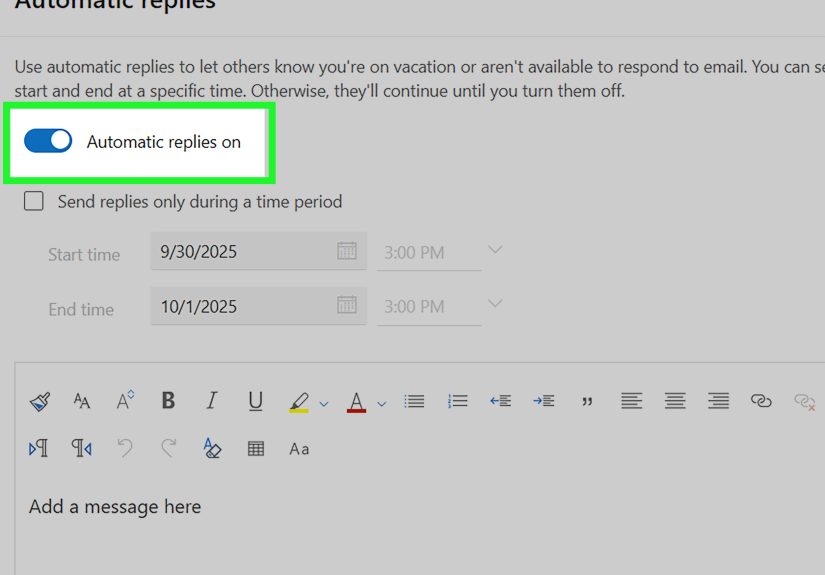
Method 1: Turn Off WebRTC in about:config
- Open Firefox.
- Type about:config in the address bar and press Enter.
- Accept the warning page if Firefox shows one.
- Search for media.peerconnection.enabled.
- Toggle the value to false.
- Restart Firefox, then run a WebRTC leak test to confirm the change.
This is the classic Firefox WebRTC setting, and it remains the closest thing to a real browser-level off switch. If your goal is to disable WebRTC in Firefox without adding another extension to your browser like a decorative throw pillow, this is the cleanest route.
Method 2: Block Camera and Microphone Requests Too
If you want extra control, also lock down site permissions:
- Go to Settings.
- Open Privacy & Security.
- Scroll to Permissions.
- Open Camera and Microphone settings.
- Remove old exceptions and enable the option to block new requests.
This does not replace the about:config tweak, but it adds another layer of protection. It is especially useful if you sometimes turn WebRTC back on for a meeting and do not want every random site auditioning for microphone access.
Firefox Pros and Cons
Pros: Firefox gives you the clearest native path to disabling WebRTC. It is friendly to privacy-conscious users and far less annoying than hunting through disappearing browser flags.
Cons: Some communication features will stop working. Also, if you use Firefox on mobile, the same level of control may not be as easy to access in every build.
How to Disable WebRTC in Chrome in 2025
Now for the messy part. If you came here hoping Chrome still has a neat little “Disable WebRTC” toggle in regular settings, I regret to inform you that Chrome prefers nuance, enterprise controls, and extension-based workarounds over simple happiness.
Translation: in standard Chrome, there is no clean consumer-facing switch that fully disables WebRTC the way Firefox does.
Method 1: Block Camera and Microphone Access
If your real goal is to stop websites from using WebRTC-heavy features such as browser calling, the most practical move is to block camera and microphone access:
- Open Chrome.
- Go to Settings.
- Select Privacy and security.
- Open Site settings.
- Under Permissions, open Camera and Microphone.
- Set them to the most restrictive option that fits your needs, and remove any sites you previously allowed.
This does not fully disable the WebRTC engine, but it blocks the most common real-world uses of it. For many users, that is enough. If you never make browser calls, this method takes a large bite out of the problem with minimal fuss.
Method 2: Limit WebRTC Exposure Instead of Fully Disabling It
Chrome’s modern approach is more about IP-handling policy than a giant red OFF button. Advanced users, admins, or privacy extensions can use Chrome’s privacy controls to limit how WebRTC routes traffic and how much local address information gets exposed.
In plain English: Chrome is much better at restricting WebRTC than at eliminating it for regular users.
Your practical options are:
- Use a reputable privacy extension that manages WebRTC behavior.
- Use a VPN or browser extension with WebRTC leak protection.
- If you are on a managed work or school device, ask the administrator whether a WebRTC IP handling policy is already enforced.
What Not to Waste Time On
A lot of old blog posts still tell users to dig through chrome://flags and flip mysterious toggles with names that sound like rejected sci-fi episode titles. In 2025, many of those instructions are outdated, renamed, missing, or inconsistent across versions. If a tutorial looks like it was written when everyone still argued about fidget spinners, do not trust it with your browser privacy.
Chrome Pros and Cons
Pros: Easy permission controls, strong extension ecosystem, and plenty of VPN tools that help prevent leaks.
Cons: No simple native full-disable switch for most regular users. Chrome is the browser equivalent of saying, “I did not say no, but I did hide the answer behind three menus and a policy page.”
How to Disable WebRTC in Opera in 2025
Opera is Chromium-based, which means its WebRTC story feels very familiar. If Chrome is the cousin who complicates everything, Opera is the cousin who complicates everything but with a built-in ad blocker and stronger opinions about aesthetics.
As with Chrome, Opera does not give most users a simple modern built-in switch to fully disable WebRTC at the browser level. The realistic strategy is to block WebRTC-dependent site access, use privacy controls, and rely on a WebRTC-focused extension or a good VPN when needed.
Method 1: Block Camera and Microphone Access in Opera
- Open Opera.
- Go to Settings.
- Open Advanced, then Privacy & security.
- Select Site settings.
- Open Camera and Microphone.
- Disable requests or remove previously allowed sites.
This is the most sensible default method for users who do not want websites initiating browser-based calls or media access.
Method 2: Use an Opera WebRTC Control Extension
Opera’s add-on catalog still includes WebRTC-focused tools such as WebRTC Control and similar privacy extensions. These are useful if your goal is not just to stop calls, but to actively reduce WebRTC-based IP exposure in a Chromium-style browser.
That said, extensions are not magic. A sloppy extension can cause site breakage, conflict with video tools, or stop something important right before a meeting, which is exactly when your boss decides to ask where you are. So choose carefully, test after installation, and disable the extension temporarily when a site absolutely needs real-time communication.
Opera Pros and Cons
Pros: Easy permission controls, useful privacy tools, and available WebRTC-focused extensions.
Cons: Like Chrome, Opera is more about controlling WebRTC than fully killing it natively for most users.
How to Test for a WebRTC Leak
Whatever browser you use, do not just change a setting, whisper “mission accomplished,” and walk away. Test it.
- Find your normal public IP address with your VPN off.
- Turn on your VPN if you use one.
- Open a trusted WebRTC leak test page.
- Check whether the IP shown matches your real IP or your VPN IP.
- Repeat in every browser you actually use, because WebRTC behavior can vary by browser.
If your real IP still appears, something is leaking. At that point, you have three likely fixes: tighten browser permissions, use a better WebRTC-blocking extension, or switch to a VPN with stronger leak protection.
Should You Fully Disable WebRTC or Just Limit It?
The answer depends on how you use your browser.
If you never use browser-based calls
Go aggressive. Disable WebRTC in Firefox. In Chrome and Opera, block camera and microphone access, remove allowed sites, and use a privacy extension if needed. You probably will not miss anything.
If you use web meetings occasionally
Consider a split setup. Keep Firefox locked down for private browsing and use Chrome or Opera only when you need a meeting platform. It is not glamorous, but it is effective. Many privacy nerds quietly do this and pretend it is a grand strategy instead of simple laziness.
If you live in browser-based communication tools
Do not fight reality. Instead of fully disabling WebRTC everywhere, use a reputable VPN with leak protection, keep site permissions tight, review allowed camera and microphone sites regularly, and run leak tests once in a while. That gives you privacy without turning every workday into a troubleshooting hobby.
Real-World Experience: What It Actually Feels Like to Disable WebRTC in 2025
In day-to-day use, disabling WebRTC feels very different depending on the browser. Firefox gives you the most satisfying privacy experience because the change is fast, obvious, and easy to verify. You flip media.peerconnection.enabled to false, restart, run a leak test, and there is a lovely sense of closure. It is one of those rare browser privacy tasks that does not require six tabs, two forums, and a brief existential crisis.
But Firefox also teaches the fastest lesson: privacy settings have consequences. The first time many users disable WebRTC and then try to jump into a browser meeting, something suddenly refuses to load, a call button does nothing, or screen sharing turns into interpretive dance. That does not mean Firefox is broken. It means the switch actually worked. If you use Firefox as a privacy-first browser and keep another browser for meetings, the experience is excellent. If Firefox is your everything browser, you will probably end up toggling the setting back on more often than expected.
Chrome feels less clean. You can tighten permissions, remove site access, install an extension, and reduce leak exposure, but it rarely feels like a complete “off” state. It feels more like reducing the number of open windows in a house during a rainstorm. Better? Absolutely. Perfect? Not really. Still, for users who mainly care about stopping websites from grabbing the camera and microphone, Chrome’s permission controls are simple and effective. If you combine them with a trustworthy VPN that includes WebRTC leak protection, Chrome becomes much more manageable.
Opera lands in a similar place. The experience is practical, not elegant. Because Opera is Chromium-based, a lot of the same logic applies: use strict permissions, add a WebRTC-focused extension if privacy is your top priority, and verify everything with a leak test. The good news is that Opera users often already like built-in privacy features, so adding one more layer does not feel unusual. The bad news is that extension-heavy setups can sometimes cause weird behavior on communication platforms, especially if you forget the extension is running and then try to join a call five minutes before something important.
The biggest real-world takeaway is this: fully disabling WebRTC is best for people who rarely need it. If you mostly browse, research, shop, stream, or write, shutting it down makes sense. If your work or school happens in the browser, a smarter long-term setup is usually controlled permissions plus VPN leak protection instead of permanent disablement.
Another practical lesson is that privacy is never one setting. Disabling WebRTC can help reduce one specific risk, but it will not make you invisible online. Cookies, browser fingerprinting, account logins, location permissions, sloppy extensions, and weak VPNs can still undo your good intentions in a hurry. Think of WebRTC hardening as one strong move in a much bigger privacy game, not a silver bullet with a cape.
And finally, there is the emotional truth no tutorial tells you: after you disable WebRTC, you will absolutely forget you did it. Not today. Not tomorrow. But one random Tuesday, when a site refuses to start your microphone, you will stare at your browser like it personally betrayed you. Future you deserves a note, a bookmark, or at least a tiny memory that says, “No, the browser is not haunted. You did this on purpose.”
Final Verdict
If you want the easiest way to disable WebRTC in 2025, Firefox wins. It still offers the most direct native route through about:config. Chrome and Opera are more complicated. In those browsers, the realistic path is to block camera and microphone access, reduce WebRTC exposure with extensions or policy-based controls, and use a VPN that handles leaks properly.
So the short version is this: Firefox lets you shut the door. Chrome and Opera mostly let you install better locks, close the curtains, and add a security camera. Not quite the same thing, but still a big improvement when done right.