Table of Contents >> Show >> Hide
- The Cautionary Tale, Reconstructed (Because This Happens More Than You’d Think)
- Why “Delete Everything” Is the Worst Offboarding Strategy Ever Invented
- Real-World Echoes: When Data Deletion (or Missing Safeguards) Went Sideways
- What Should Have Happened Instead: A Smart, Boring, Highly Effective Offboarding Plan
- Backups That Can’t Be “Oops-ed” Away
- How to Prevent One Person From Having “Delete the Company” Power
- Managerial Lesson: Don’t Turn IT Offboarding Into a Power Move
- Quick Offboarding Checklist (Print This Before Someone Prints Their Resignation)
- of “This Is What It Feels Like” Experiences From the Real World
There are two kinds of managers in the world: the ones who treat IT like a partner, and the ones who treat IT like a vending machine that occasionally
refuses to dispense the “fix my problem” snack. This story is about the second kindspecifically, the kind who thinks, “I’ll show them who’s in charge,”
while standing within arm’s reach of the company’s entire digital life.
If you’ve ever worked around systems administration, you’ve probably heard a version of this cautionary tale: a boss fires the IT person, then orders
them to “delete everything” (or “wipe your stuff” or “remove your access and take your files with you”), even after someoneHR, Legal, Security, or the
one person in the meeting who reads the warning labelssays, “Maybe don’t do that.”
The punchline is always the same: the boss realizes the mistake too late. The only thing that loads quickly now is regret.
The Cautionary Tale, Reconstructed (Because This Happens More Than You’d Think)
Picture a mid-sized company with big dreams, a busy sales team, and exactly one person who knows where the “important spreadsheet” lives. That person is
the IT adminlet’s call him Alexwho built the file server structure, managed cloud accounts, handled backups (when budget allowed), and kept a mental map
of all the weird “temporary” workarounds that somehow became permanent.
One day, a senior managerlet’s call him Brad, because the universe insistsdecides Alex is “too expensive,” “too cautious,” or “not a culture fit”
(translation: Alex said “no” to a risky request). Brad fires Alex and then adds a flourish: Alex must immediately delete all the files he “owns” and
remove anything he “touched.” Brad wants a clean break. A symbolic reset. A dramatic keyboard slam.
Someone warns Brad that this is a bad idea. Possibly several people. Brad interprets “bad idea” as “challenge” and doubles down. Alex, now terminated,
is still sitting at the admin console because Brad wants this done right now.
Minutes later, shared drives vanish. Project folders evaporate. “Final_FINAL_v7_reallyfinal.xlsx” becomes a legend. Suddenly, nobody can log into the CRM,
invoices don’t generate, the warehouse can’t print labels, and the CEO’s calendar looks like a crime scene.
Brad learns a valuable lesson: when you hand someone the keys and say “burn it down,” you don’t get to act shocked when smoke appears.
Why “Delete Everything” Is the Worst Offboarding Strategy Ever Invented
Let’s be clear: employers can and should control company data. But ordering deletions during a termination is like trying to “tidy up” a library by
lighting a match and calling it minimalism. Here’s why this goes wrong so reliably.
1) Termination Is a Security Event, Not a To-Do List Item
When someone leavesespecially under adverse or involuntary circumstancesaccess must be handled quickly, consistently, and with documented steps.
This isn’t drama; it’s risk management. A termination changes trust boundaries immediately. The correct move is to revoke access, preserve needed data,
and transfer ownership under controlled administrative processes. The incorrect move is to improvise in real time while emotions are still in the room.
2) “Ownership” of Digital Work Is Complicated (And Your Tools Enforce That)
In modern systems, files aren’t just “yours.” They’re shared, permissioned, linked, synced, and referenced by automation. A folder deletion can break
workflows that depend on that path. Removing a user can orphan cloud documents. Deleting a mailbox can erase institutional knowledgeunless retention is
configured. Offboarding is less like packing a desk and more like rerouting a city’s plumbing.
3) Legal, Compliance, and Audits Hate Surprise Deletions
Companies often have retention obligationscontracts, HR records, financial documentation, customer communications, and electronically stored information
potentially relevant to disputes. If you delete first and ask Legal later, you may create compliance problems that cost far more than any single employee.
Even when deletion is allowed, the timing, scope, and documentation matter.
4) Your Backups Might Not Be What You Think They Are
The most common phrase during a data-loss incident is: “We have backups.” The second most common phrase is: “Wait… do we?”
Backups fail silently. Credentials expire. Jobs stop running. Storage fills. And restore procedures are often untested until the day you need themwhen
the clock is loud, customers are calling, and everyone suddenly becomes deeply interested in the difference between “snapshot,” “replica,” and “backup.”
Real-World Echoes: When Data Deletion (or Missing Safeguards) Went Sideways
The “boss orders deletion” story is a spicy version of a broader truth: organizations get hurt when too much power is concentrated, processes are informal,
and recovery isn’t tested. Here are three real-world cautionary patterns worth knowing.
Insider sabotage and the “logic bomb” nightmare
Insider risk is not a movie plotit’s a known category of threat. In one widely discussed case from the 1990s, an employee planted malicious code that
detonated after termination, damaging systems and disrupting operations. The key takeaway isn’t the sensational detail; it’s the boring lesson: access,
monitoring, and separation procedures matter most when relationships break down.
External compromise that erased production and backups
Another pattern: attackers gain control of privileged cloud accounts and delete infrastructure and backups. When the same credentials can manage production
systems and destroy recovery points, the blast radius becomes existential. “Full redundancy” doesn’t help if someone can delete the redundant parts.
Accidental deletion + untested recovery = long day, short data
Sometimes there’s no villainjust a sequence of normal human mistakes and safeguards that weren’t ready. Public postmortems from technology companies have
shown how a single deletion can cascade into hours of data loss when backups aren’t fully verified or restore steps are complex under pressure.
What Should Have Happened Instead: A Smart, Boring, Highly Effective Offboarding Plan
If your offboarding process is “figure it out live in the termination meeting,” you’re not offboardingyou’re improvising with production systems.
A mature employee offboarding plan treats identity and access management like an assembly line: predictable, repeatable, and hard to mess up.
Step 1: Freeze the Situation (Before Anyone Touches Anything)
- Restrict privileged access immediately (disable sign-in, revoke sessions, rotate shared credentials).
- Preserve data first: mailbox holds/retention, file snapshots, and project exports where appropriate.
- Document who requested what, when, and why (yes, even if it feels awkward).
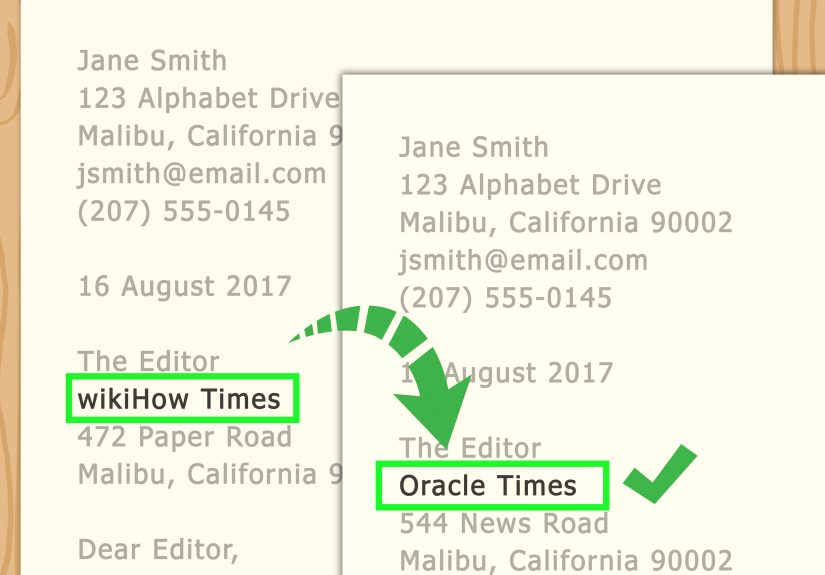
Step 2: Transfer Ownership and Knowledge the Right Way
In cloud suites, you typically want to transfer ownership of files and give managers access to the former employee’s work artifactswithout keeping the
former employee’s account active longer than necessary. Many platforms provide official “remove a former employee” flows that emphasize preserving and
transferring data before deletion.
- Email: Convert to a retained state (inactive mailbox, retention policies, or legal hold if required) and grant access only to authorized roles.
- File storage: Transfer drive ownership, reassign shared folders, and verify shared links and team permissions still work.
- Devices: Collect hardware, wipe under policy, and confirm endpoint management keys and certificates are revoked.
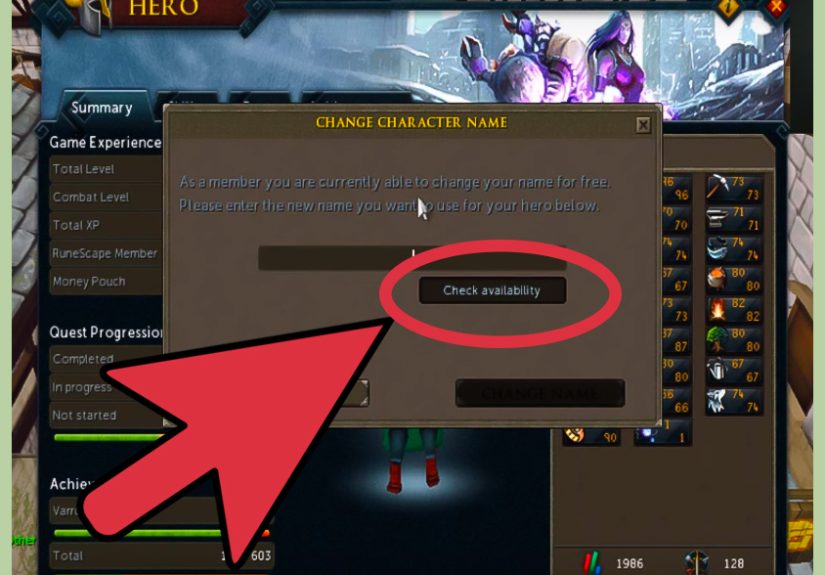
Step 3: Deprovision Everywhere (Not Just the “Main” Account)
Modern companies don’t run on one login. They run on dozens: SaaS apps, VPN, code repositories, marketing platforms, payroll tools, cloud consoles, and the
odd “temporary” admin account created during an outage two years ago and never removed.
This is where automated provisioning and deprovisioning shine: HR status changes can trigger access revocation across connected systems, creating a clear
audit trail and reducing the “we forgot that one tool” problem.
Step 4: Rotate Secrets Like You Mean It
Shared passwords are the glitter of cybersecurity: once they’re out, they’re everywhere, and you’ll be finding sparkles for months. After termination:
- Rotate shared credentials (service accounts, vendor portals, social media accounts, API keys).
- Review privileged groups and remove the user from all admin roles.
- Invalidate MFA methods tied to the user, including recovery options.
Backups That Can’t Be “Oops-ed” Away
If you want to survive a bad daywhether it’s a mistaken deletion, a malicious act, or ransomwareyou need a backup strategy that assumes your worst day
will be impressively creative.
The 3-2-1 Rule (And Why People Keep Recommending It)
The classic guideline: keep three copies of your data, on two different media types, with one copy stored offsite. It’s popular because it’s simple and
it works across businesses of all sizes. The goal is resilience against single points of failure: one broken server, one accidental wipe, one building
incident, one compromised admin account.
Modern Upgrade: Immutable or “Write-Once” Backups
Today’s threat landscape includes attackers who specifically target backups. That’s why immutable backupscopies that can’t be modified or deleted for a
retention periodhave become a key part of cyber resilience. If someone can’t delete the recovery points, you can recover even after a messy incident.
Test Restores or Accept That You Don’t Actually Have Backups
A backup you’ve never restored is a hopeful rumor. Schedule test restores. Document the steps. Time them. If you can’t restore under calm conditions, you
won’t restore under chaos.
How to Prevent One Person From Having “Delete the Company” Power
This is where governance beats heroics. The goal isn’t to distrust employees; it’s to design systems that are safe even when humans are stressed, rushed,
or leaving the organization.
Least Privilege, Seriously
Least privilege means users and processes have only the minimum access needed to do their jobs. Not “all the access, just in case.” Not “temporary admin,
but forever.” Least privilege reduces accidental damage and limits the blast radius of misuse.
Separate Duties and Add Guardrails for Destructive Actions
- Require approvals for mass deletion or permission changes in critical environments.
- Use dedicated break-glass accounts with strong MFA, stored securely, and monitored heavily.
- Log admin actions and review themespecially around termination events.
Make Offboarding a Workflow, Not a Conversation
The best offboarding checklist is the one people follow without improvisation. Pair HR + IT + Security + Legal on a clear process. Define timelines,
escalation paths, and who signs off on data deletion versus data retention. A good process is boring. Boring is beautiful.
Managerial Lesson: Don’t Turn IT Offboarding Into a Power Move
The “boss orders deletion” situation often starts with ego and ends with downtime. If you manage people, here’s the practical takeaway:
- Don’t improvise with access. Use documented procedures.
- Don’t outsource your anger to the admin console. Termination is not a performance art piece.
- Don’t confuse “my authority” with “my ability to recover data.” Those are not the same skill.
- Do preserve data first. Transfer ownership, apply retention, and verify backups.
- Do involve the right teams. HR, Legal, Security, and IT each own part of the risk.
Quick Offboarding Checklist (Print This Before Someone Prints Their Resignation)
Immediate (same day)
- Disable sign-in, revoke sessions, remove from privileged groups.
- Rotate shared passwords, keys, and API tokens.
- Preserve mailbox and files (retention/hold as needed).
- Capture an inventory of systems the user had access to (including “shadow IT”).
Next 72 hours
- Transfer ownership of cloud files and shared resources.
- Reassign tickets, projects, and operational responsibilities.
- Verify backups and run a test restore for critical data.
- Review logs for unusual access around termination time.
Within 30 days
- Decommission accounts that are no longer needed.
- Audit privileges and remove stale admin access.
- Document lessons learned and update the checklist.
of “This Is What It Feels Like” Experiences From the Real World
Ask a room full of IT people about offboarding horror stories and you’ll see the same facial expression appear, like a synchronized swimming routine made
entirely of exhaustion. The stories differ in detailson-prem vs. cloud, big company vs. scrappy startup, calm resignation vs. messy terminationbut the
emotional arc is remarkably consistent: someone treats access like a light switch, flips it with zero planning, and then acts surprised when the building
goes dark.
One common “experience pattern” goes like this: leadership wants speed and certainty (“Make it immediate!”), while IT wants sequence and safety (“Preserve,
transfer, then remove.”). The tension escalates when a manager assumes offboarding is just deleting a user, the way you delete a contact from your phone.
The reality is that a departing employee’s account is often the glue holding together shared calendars, automated alerts, vendor logins, scheduled jobs,
and that one mailbox rule that quietly routed customer complaints to the right team. When you pull the account without planning, you don’t just remove a
personyou remove a set of hidden dependencies.
Another recurring theme is the “mystery of the missing owner.” Teams discover that a critical folder was owned by a single user account, and nobody
thought to transfer ownership because “the folder is shared anyway.” Then the account is deleted and suddenly permissions behave differently, links break,
or compliance features lock content behind admin roles that weren’t assigned. The fix is usually straightforwardtransfer ownership, apply retention, set
up archive accountsbut the timing is painful: it always happens while a deadline is on fire.
The most stressful experiences come from the backup illusion. People confidently say, “We have backups,” until someone tries to restore and discovers the
backup set is incomplete, encrypted by an attacker, stored in the same place as production, or simply never tested. That’s when the tone in the room
changes. Offboarding mistakes are annoying; un-recoverable data loss is existential. It impacts customers, revenue, and reputationsand it forces teams to
choose between rebuilding from scratch or explaining to stakeholders why “we thought it was backing up” is not the same as “we can restore.”
The best experiencesyes, good ones existcome from organizations that treat offboarding as a workflow with muscle memory. HR triggers the process, IT
runs a checklist, security reviews privileged access, and legal flags retention requirements. Nobody argues in the moment because the decisions were made
ahead of time. The departing employee is treated respectfully, access is removed promptly, data is preserved appropriately, and the business keeps moving.
It’s not dramatic, so nobody writes a viral post about itand that’s exactly the point. The goal isn’t a story. The goal is an uneventful Tuesday.