Table of Contents >> Show >> Hide
- Why a Voided Check Still Deserves VIP Security
- What Information Is on a Voided Check?
- When Is It Reasonable to Send a Voided Check?
- Best Way to Scan a Voided Check Safely
- Is Email Safe for Sending a Voided Check?
- Safer Alternatives to Emailing a Voided Check
- How to Email a Voided Check More Safely
- Common Mistakes to Avoid
- What to Do If You Sent a Voided Check to the Wrong Email
- Special Tips for Employers and Small Businesses
- Real-World Experiences: What People Learn the Hard Way
- Conclusion
- SEO Tags
Note: This article is for general educational purposes and does not replace advice from your bank, employer, payroll provider, or financial institution.
Why a Voided Check Still Deserves VIP Security
A voided check looks harmless. After all, you wrote “VOID” across the front in letters large enough to be seen from space. Surely nobody can use it to buy a yacht, right? Not exactly. While the word “VOID” helps prevent the check from being cashed as a normal payment, the document still contains sensitive financial information: your name, bank name, routing number, account number, and sometimes your address.
That information is exactly why employers, payroll departments, government agencies, payment processors, and vendors often ask for a voided check. They use it to confirm where money should be deposited or withdrawn. The same details that help your paycheck arrive safely can also create headaches if they land in the wrong inbox, on the wrong shared computer, or in the digital hands of someone who thinks “fraud” is a career path.
Scanning and emailing voided checks safely is about reducing risk. It is not about panic. People send financial documents every day, and most of the time nothing dramatic happens. But when a voided check is mishandled, it can lead to unauthorized electronic transfers, fake checks, account compromise, payroll fraud, or identity-theft problems that are about as fun as stepping on a Lego while carrying coffee.
What Information Is on a Voided Check?
Before sending a voided check by email, understand what you are actually sharing. A standard personal check usually includes several pieces of information that help financial systems move money accurately.
Routing Number
The routing number is the nine-digit number that identifies your bank or credit union. It tells the payment network where the money should go first. Routing numbers are not secret in the same way passwords are secret, but they become sensitive when paired with your account number and personal details.
Account Number
Your account number identifies your specific checking account. Combined with the routing number, it can be used to set up direct deposit, automatic bill payments, ACH transfers, or account verification. This is the “handle with care” part of the check.
Name, Address, and Signature Area
Some checks show your address, phone number, or other personal details. If the check was previously signed before being voided, the image may also expose your signature. That combination of data can make social engineering easier. In plain English: a scammer may use real information about you to sound more believable.
Check Number
The check number is usually less sensitive than the account number, but it can still help someone imitate the appearance of a legitimate check. If possible, avoid sending more check details than the recipient truly needs.
When Is It Reasonable to Send a Voided Check?
There are legitimate reasons to provide a voided check. The most common is direct deposit. Employers and payroll services often need your bank name, routing number, account number, account type, and authorization to deposit wages. Some vendors or billing departments may request similar information to set up ACH payments. Tax refunds, benefits, and reimbursement systems may also rely on bank account information.
Still, “someone asked for it” is not enough. Before scanning and emailing a voided check, confirm that the request is real, necessary, and being sent through a secure process. A legitimate payroll department will not be offended if you ask, “Can I upload this through a secure portal instead?” In fact, the serious ones may smile proudly, like a cybersecurity parent watching their child use a password manager.
Best Way to Scan a Voided Check Safely
If you truly need to send a voided check, start with a clean, careful scan. Your goal is to create a readable document without exposing unnecessary details or leaving copies scattered across devices.
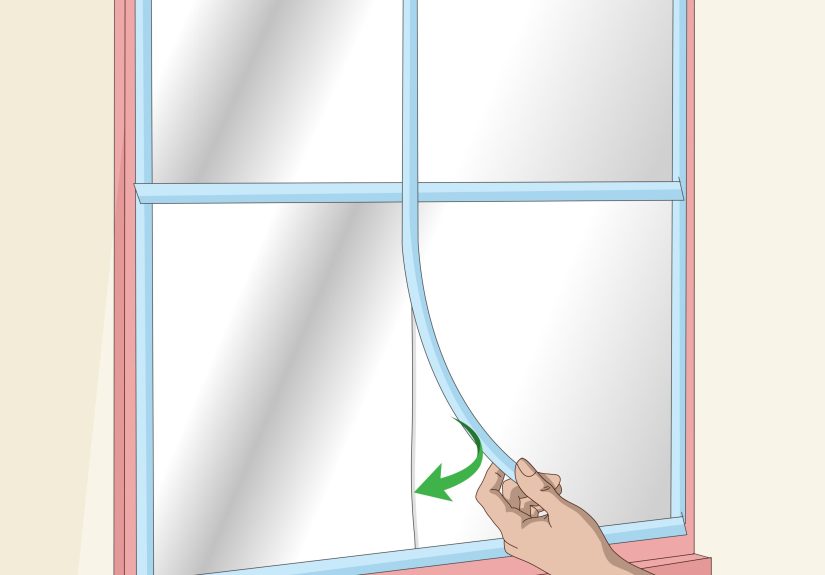
Step 1: Write “VOID” Clearly Across the Check
Use dark ink and write “VOID” across the front of the check in large letters. Do not cover the routing number or account number if the recipient needs those details. Avoid signing the check. A voided check does not need your signature for direct deposit setup.
Step 2: Use a Trusted Device
Scan the check using your own scanner, secure mobile banking app, or trusted phone. Avoid public printers, hotel business centers, school computers, library scanners, or random office machines that store document histories. Public devices are convenient, but so is eating cereal from a mixing bowl. Convenient does not always mean wise.
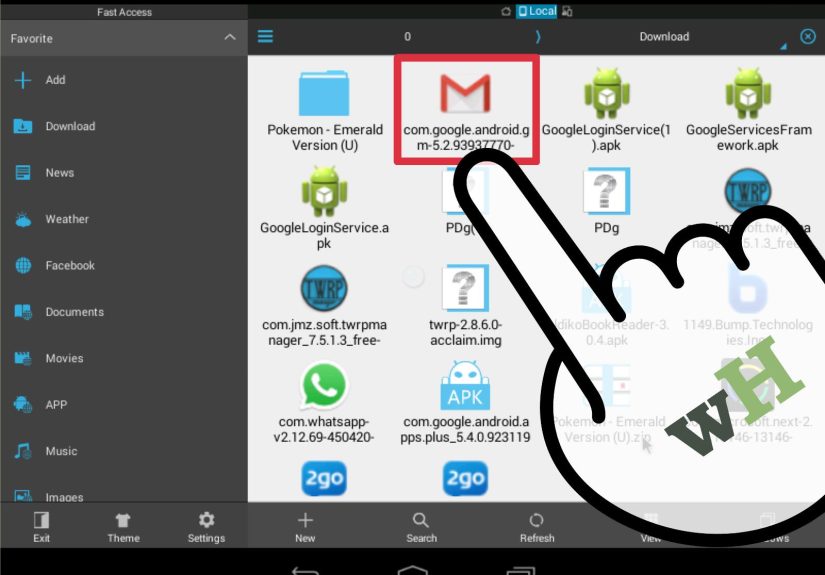
Step 3: Save It as a PDF
A PDF is usually easier to protect, share, and open than an image file. Give it a clear but not overly revealing name. For example, “Direct_Deposit_Form.pdf” is better than “My_Chase_Checking_Account_9876_Voided_Check.pdf.” File names can be seen in inboxes, downloads, backups, and previews.
Step 4: Crop Out Anything Unnecessary
If the recipient only needs the bottom banking line and your printed name, consider asking whether a direct deposit form from your bank would work instead. If you must send the check image, do not include extra pages, statements, envelopes, or unrelated financial documents.
Step 5: Store It Temporarily
Do not leave the scan sitting forever on your desktop, camera roll, cloud folder, or downloads folder. After the recipient confirms it was received and processed, delete unnecessary copies. Also empty your computer’s trash or recently deleted folder. A file is not truly gone just because it has been moved to digital purgatory.
Is Email Safe for Sending a Voided Check?
Regular email is not the safest way to send sensitive financial information. Standard email can pass through multiple servers, remain in sent folders, sit in the recipient’s inbox, and be forwarded accidentally. Attachments can also be downloaded to devices you do not control.
If the recipient offers a secure upload portal, use it. A secure portal usually requires login credentials, encrypts data in transit, limits access, and stores documents in a controlled system. Many banks, payroll companies, mortgage lenders, and HR platforms provide document-upload tools for this reason.
If email is the only option, reduce the risk. Confirm the recipient’s email address through a trusted channel. Use password protection when possible. Send the password separately, such as by phone or secure message, not in the same email as the attachment. Keep the email brief and avoid adding extra personal details.
Safer Alternatives to Emailing a Voided Check
Before you attach a scanned voided check to an email, ask whether one of these safer alternatives is accepted.
Use a Bank Direct Deposit Form
Many banks and credit unions provide official direct deposit forms through online banking. These forms often include the routing number, masked account details, bank name, and account owner information. Some are designed specifically for payroll setup and may be safer than sending a full check image.
Use a Secure Payroll Portal
If you are setting up payroll, your employer may use a provider that allows employees to enter banking details directly. This avoids sending a document through email and may reduce manual entry errors.
Provide Details in Person
For local employers or institutions, submitting the form in person may be safer than email. Use a sealed envelope and give it only to the authorized department. Do not hand it to “that one guy near the copier” unless that guy is actually payroll.
Ask Your Bank for an Account Verification Letter
Some banks can provide a letter confirming your account information for direct deposit. This may satisfy the requester without exposing a check image. Requirements vary, so ask both your bank and the organization requesting the document.
Use a Secure Message Center
Banks, lenders, and some financial platforms have secure message centers after login. These are typically better than normal email because access is restricted to authenticated users.
How to Email a Voided Check More Safely
If you cannot avoid email, take a careful approach. The goal is not perfection. The goal is to avoid obvious mistakes that turn a routine task into a fraud-prevention seminar starring you.
Verify the Request First
Call the organization using a phone number from its official website, your employee handbook, your bank statement, or a known contact. Do not rely only on a phone number inside the email requesting the check. Scammers love urgent messages, fake HR emails, and “please send this today” pressure.
Check the Email Address Carefully
Look for misspellings, extra letters, strange domains, or free email accounts pretending to represent a business. For example, [email protected] is not the same as [email protected]. One looks official; the other looks like it was assembled during a lunch break.
Use Password Protection
If you create a password-protected PDF, choose a strong password. Do not use your birthday, pet’s name, school mascot, or “password123,” which is less a password and more a welcome mat. Send the password through a separate channel, such as a phone call or secure text to a verified contact.
Do Not Include Extra Sensitive Information
Your message should be simple. Do not add your Social Security number, debit card number, online banking password, PIN, or security questions. A voided check is already sensitive enough. No need to turn the email into a buffet for identity thieves.
Use a Secure Network
Avoid sending sensitive documents over public Wi-Fi unless you are using a trusted VPN and secure connection. Home internet or a trusted mobile connection is usually a better choice than airport Wi-Fi named “Free_Coffee_WiFi_Definitely_Not_A_Hacker.”
Confirm Receipt
After sending the document, ask the recipient to confirm receipt. Once it is processed, ask whether they can delete the email attachment or whether their organization retains it under a formal document policy. You may not control their retention rules, but asking shows that you take financial privacy seriously.
Common Mistakes to Avoid
Small mistakes can create big problems when financial documents are involved. Here are the most common ones.
Sending to the Wrong Person
Autocomplete is helpful until it sends your voided check to “Pam from pickleball” instead of “Payroll.” Always double-check the recipient before clicking send.
Using a Shared Email Account
Do not send a voided check from an account shared with friends, classmates, roommates, or family members unless absolutely necessary. Shared access means shared risk.
Leaving the File in Cloud Storage
If your phone automatically backs up images to the cloud, your check scan may be stored in more places than you realize. Delete extra copies from photo apps, cloud folders, downloads, and email drafts.
Sending a Blank Check Instead of a Voided Check
Never send a blank check image. Always void it first. A blank check is not a document; it is a financial jump scare.
Ignoring Account Monitoring
After sending any bank document, monitor your checking account. Set up alerts for withdrawals, transfers, low balances, and unusual activity. Early detection can make a major difference if something goes wrong.
What to Do If You Sent a Voided Check to the Wrong Email
Accidents happen. If you sent a scanned voided check to the wrong person, act quickly and calmly.
Contact Your Bank
Tell your bank or credit union that your account and routing information may have been exposed. Ask what protections are available. They may recommend monitoring, placing alerts, closing the account, opening a new account, or blocking certain types of transactions.
Ask the Recipient to Delete It
If the wrong recipient is known and trustworthy, ask them to delete the email and attachment from their inbox, downloads, and trash folder. This is not a complete guarantee, but it is still worth doing.
Change Related Logins
If your email account may have been compromised, change your email password immediately and enable multi-factor authentication. Also update passwords for online banking and payroll portals.
Watch for Unauthorized Transfers
Review your account activity frequently. Report suspicious transactions to your financial institution immediately. Consumer protections may depend on how quickly you report unauthorized activity, so do not wait for “future you” to handle it. Future you is busy and probably forgot.
Report Identity Theft or Fraud
If your information is misused, report identity theft or fraud through the appropriate official channels and follow your bank’s recovery process. Keep records of dates, names, transaction numbers, emails, and screenshots.
Special Tips for Employers and Small Businesses
Businesses should avoid asking employees, contractors, tenants, or vendors to email voided checks casually. A better process protects everyone.
Use Secure Collection Tools
Payroll and accounting teams should use secure portals, encrypted forms, or verified payment platforms. A shared inbox full of bank documents is not a security strategy. It is a filing cabinet with the lock made of spaghetti.
Limit Access
Only employees who truly need banking documents should be able to view them. Access should be role-based, logged, and removed when staff change positions or leave the company.
Train Staff to Spot Fraud
Business email compromise, fake vendor changes, and payroll redirection scams often begin with one convincing message. Train employees to verify changes to bank information through a second channel before updating payment details.
Delete What You No Longer Need
Companies should follow written retention policies. Keeping sensitive documents forever “just in case” increases exposure. Keep what is required, protect it properly, and securely dispose of what is no longer needed.
Real-World Experiences: What People Learn the Hard Way
In real life, the risky part of scanning and emailing voided checks is rarely the scanning itself. The risky part is the casual attitude around it. Many people treat a voided check like a receipt from a sandwich shop: useful for two minutes, then forgotten. But a voided check is closer to a backstage pass to your checking account. It may not let someone instantly drain your funds, but it gives them enough information to attempt mischief, impersonation, or unauthorized payment setup.
One common experience involves new employees rushing through onboarding. HR sends a stack of forms, the employee wants the first paycheck to arrive on time, and suddenly a voided check is photographed under bad kitchen lighting and emailed from a phone. The photo may remain in the camera roll, sync to a cloud account, sit in the sent folder, and appear as a thumbnail in a messaging app. The employee thinks the task is finished. The file thinks it has moved into a permanent digital condo.
A better habit is to create a mini-process. First, confirm the payroll method. Second, ask whether the employer accepts a secure portal or bank-generated direct deposit form. Third, send only what is needed. Fourth, delete the local copy after confirmation. These steps take a few extra minutes, but they prevent the “Where did I save that?” problem later.
Another real-world issue is email forwarding. A person may send a voided check to one trusted contact, but that contact forwards it to payroll, accounting, a manager, and possibly someone named “Operations Inbox.” Every forward creates another copy. None of those people may be dishonest, but each inbox becomes another place where the attachment could be exposed through a weak password, lost device, or accidental forwarding chain. The safest document is not the one forwarded politely through seven inboxes. It is the one uploaded once to the correct secure system.
Small businesses often learn this lesson during vendor setup. A vendor emails new payment details, and the business updates the account without confirming by phone. Later, the real vendor asks why the invoice was never paid. The business discovers the email was fake or intercepted. While this example may involve ACH instructions rather than a voided personal check, the lesson is the same: bank information changes should always be verified through a trusted contact method. Email alone is not enough.
Families run into similar problems when helping older relatives set up benefit payments, rent transfers, or caregiver reimbursements. A well-meaning family member may scan a check and send it to several people “to be helpful.” The safer approach is to appoint one trusted person to handle the document, use the official portal whenever available, and keep a simple record of where the information was submitted.
Students and first-time workers also benefit from learning this early. Direct deposit is normal, but sending banking details should never feel casual. Treat a voided check like a financial document, not a homework attachment. Verify the request, protect the file, avoid public Wi-Fi, use strong passwords, and keep copies under control.
The best experience is boring: you submit the right document through the right channel, your paycheck arrives, your account stays quiet, and no one has to call the bank while stress-eating cereal at midnight. In financial security, boring is beautiful.
Conclusion
Scanning and emailing voided checks safely comes down to one simple principle: share the least amount of sensitive information through the safest available channel. A voided check may not be cashable, but it still contains banking details that deserve careful handling. Before emailing it, ask for a secure portal or bank-issued direct deposit form. If email is unavoidable, verify the recipient, protect the file, use a secure network, and clean up extra copies afterward.
Good financial security is not about being paranoid. It is about being just suspicious enough to avoid starring in your own fraud recovery story. Write “VOID” clearly, send carefully, monitor your account, and remember: the safest attachment is the one that does not spend the next five years living rent-free in six inboxes.