Table of Contents >> Show >> Hide
- What Is JavaScript Injection?
- Step 1: Learn Where JavaScript Injection Usually Starts
- Step 2: Treat All Input as Untrusted by Default
- Step 3: Encode Output for the Right Context
- Step 4: Sanitize HTML Only When You Truly Need HTML
- Step 5: Avoid Dangerous DOM APIs and Unsafe Rendering Habits
- Step 6: Add a Strict Content Security Policy and Trusted Types
- Step 7: Control Third-Party Scripts, Dependencies, and Supply Chain Risk
- Step 8: Test, Monitor, and Train Like This Problem Is RealBecause It Is
- Common Mistakes That Make JavaScript Injection Easier
- A Practical Example
- Experience-Based Lessons From Teams That Deal With This Problem
- Conclusion
- SEO Tags
JavaScript injection sounds like one of those phrases that can make a developer spill coffee onto a keyboard in under three seconds. And honestly, that reaction is fair. When untrusted input gets treated like executable code, websites can go from “helpful digital storefront” to “surprise security incident” faster than you can say innerHTML.
This guide is the safe, practical version of the topic. Instead of teaching anyone how to inject scripts into a page, it explains how to stop JavaScript injection before it becomes a problem. If you build, manage, review, or publish web content, these eight steps will help you reduce risk, protect users, and avoid the kind of emergency meeting nobody enjoys.
We’ll cover what JavaScript injection is, where it usually appears, which coding habits make it worse, and how to build layered defenses that actually hold up in the real world. You’ll also find examples, common mistakes, and a final section with real-world experience-based lessons that make this topic much easier to remember.
What Is JavaScript Injection?
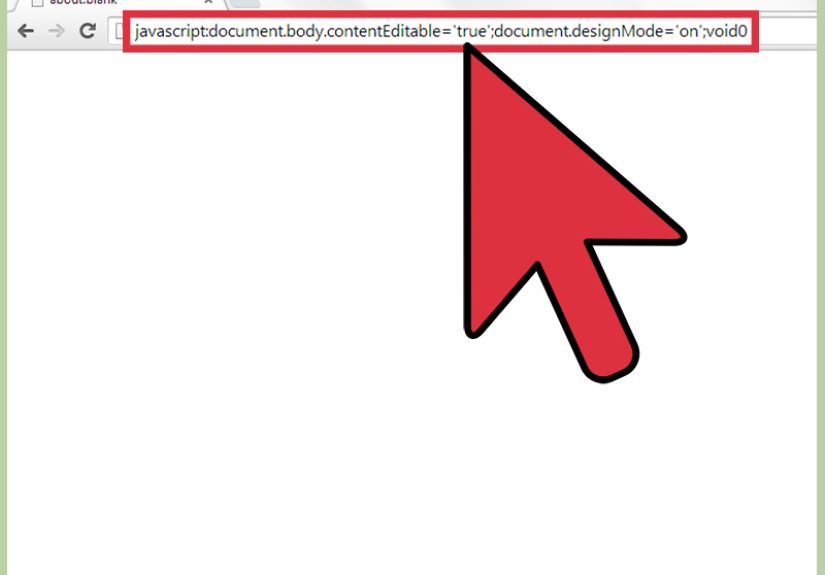
JavaScript injection happens when a web application allows untrusted content to be interpreted as executable script in the browser. In plain English, the site expects text, but the browser ends up seeing code. That can lead to stolen session data, unwanted actions, defaced content, malicious redirects, or quiet behind-the-scenes abuse of a user’s account.
In many cases, this falls under the broader category of cross-site scripting, often called XSS. The three most commonly discussed forms are reflected XSS, stored XSS, and DOM-based XSS. The names sound technical, but the root problem is simple: unsafe handling of data at the point where it is rendered or executed.
The good news is that JavaScript injection is not prevented by luck, wishful thinking, or a motivational poster in the engineering room. It is prevented by clear rules, secure defaults, careful rendering, and a healthy distrust of anything that came from users, external systems, or third-party sources.
Step 1: Learn Where JavaScript Injection Usually Starts
You cannot defend what you do not recognize. The first step is understanding the places where script injection usually begins. Common entry points include search boxes, comment forms, profile fields, URL parameters, support chat widgets, rich text editors, markdown previews, imported CSV data, analytics tags, and third-party embeds.
Developers sometimes think the problem starts with the browser. It usually starts earlier, when an application accepts data without defining how that data is supposed to behave. If a field is meant to store plain text, treat it like plain text from the moment it enters the system. If a field is allowed to contain HTML, define exactly what tags and attributes are acceptable. “We’ll clean it up later” is not a security strategy. It is a future apology.
Make an inventory of every place your application accepts content and every place it displays content. That sounds boring, and yes, spreadsheets may be involved, but it is one of the highest-value exercises a team can do. Once input sources and rendering locations are mapped, hidden risk becomes visible.
Step 2: Treat All Input as Untrusted by Default
User input is not the only untrusted input. That is the trap. Data from APIs, customer support tools, content management systems, uploaded files, query strings, browser storage, webhooks, and third-party integrations can also introduce unsafe content. If it entered your system from outside your code boundary, it deserves suspicion.
Start with validation. Validation helps confirm that input matches expected types, formats, lengths, and character rules. A ZIP code should not behave like a movie script, and a username should not need event handlers. Define strict rules for each field and reject data that falls outside the intended pattern.
That said, validation alone is not enough. Many teams validate input and then assume they are done. They are not done. Validation reduces bad input, but output handling is what stops text from becoming executable code when the browser renders it.
Step 3: Encode Output for the Right Context
Output encoding is where many JavaScript injection problems are won or lost. The same text must be handled differently depending on where it appears. Rendering data inside HTML body content is not the same as rendering it inside an HTML attribute, inside JavaScript, inside CSS, or inside a URL.
This is the classic mistake: a team escapes a value for one context and then reuses it in another. That is like wearing swim goggles to a welding job. Technically protective gear, yes. The correct protective gear, absolutely not.
Think in Rendering Contexts
If data is displayed as normal page text, use HTML encoding. If it appears inside an attribute, use attribute-safe encoding. If it becomes part of a URL, use URL encoding. If it must be inserted into JavaScript, avoid string construction when possible and use safer patterns that keep data separate from code.
Modern frameworks often help by escaping output by default. That is excellent, but only if developers do not bypass those protections. The moment someone decides to render raw markup “just this once,” the security team starts hearing dramatic violin music in the distance.
Step 4: Sanitize HTML Only When You Truly Need HTML
Sometimes an application really does need to allow limited HTML. Blog platforms, documentation tools, comment systems, and WYSIWYG editors often require formatted content. In those cases, do not try to sanitize with a few string replacements and a brave face. Use a well-maintained sanitizer and a strict allowlist.
A safe HTML policy should define which tags are allowed, which attributes are allowed, and which URL schemes are acceptable. It should block risky scripting behavior, inline event handlers, and unsafe protocol tricks. The default mindset should be “allow only what is necessary,” not “block only what looks scary.”
Also remember this: if you do not actually need rich HTML, do not allow it. Plain text is far easier to secure. Plenty of security bugs begin with a product decision that sounds harmless: “Wouldn’t it be nice if users could paste custom HTML?” Nice for users, maybe. Nice for attackers, definitely.
Step 5: Avoid Dangerous DOM APIs and Unsafe Rendering Habits
JavaScript injection often becomes a browser-side problem through unsafe DOM manipulation. If code takes untrusted content and drops it into dangerous sinks, the browser may interpret that content as active markup or script.
Safer Habits Matter
Prefer APIs and patterns that insert text rather than raw HTML whenever possible. Keep data and code separate. Use framework rendering features that escape content by default. Review places where developers are tempted to use raw HTML rendering shortcuts, especially when content comes from users or external systems.
Frameworks can help, but they are not magical force fields. React, for example, escapes text by default, but raw HTML rendering features still require extreme caution. The same goes for template overrides, custom directives, hand-built DOM updates, and quick copy-paste snippets from old tutorials that have aged like milk in the sun.
Add code review checks for unsafe rendering patterns. If your team can spot risky DOM writes early, you prevent a surprising number of production incidents.
Step 6: Add a Strict Content Security Policy and Trusted Types
A strong Content Security Policy, or CSP, acts as a backup defense. It does not replace validation, encoding, or sanitization, but it can limit the damage if unsafe content slips through. A strict CSP can help control which scripts the browser is allowed to run and make inline script execution much harder.
The strongest modern approach uses nonces or hashes rather than broad allowlists. That reduces the chance that injected code will run simply because it appears in a page. CSP is not a silver bullet, but it is an excellent second lock on the door.
Trusted Types add another layer by controlling how dangerous DOM sinks receive data. In supported environments, Trusted Types can force content to pass through approved transformation or sanitization logic before reaching high-risk APIs. That turns “maybe safe, maybe chaos” into a more enforceable engineering policy.
In other words, if secure coding is your daily habit, CSP and Trusted Types are your emergency airbag.
Step 7: Control Third-Party Scripts, Dependencies, and Supply Chain Risk
Not every JavaScript injection issue comes from your own code. Third-party scripts, browser widgets, plugins, analytics tools, old packages, and poorly maintained editors can create openings you did not expect. If you load remote scripts freely, you are effectively inviting strangers to rearrange your furniture and hoping they only fluff the pillows.
Review which external scripts are truly necessary. Remove what you do not use. Keep dependencies updated. Watch vulnerability disclosures. Pay special attention to packages that process HTML, markdown, pasted content, or template rendering, because those are common places for injection-related flaws.
Establish an approval process for third-party code. Security teams should know what is loaded, why it is loaded, and whether it can affect page rendering or user data. Convenience matters, but convenience without review is how tomorrow’s incident report gets its opening paragraph.
Step 8: Test, Monitor, and Train Like This Problem Is RealBecause It Is
The last step is ongoing discipline. JavaScript injection prevention is not a one-time checklist; it is a repeatable process. Test for unsafe rendering during development. Include security review in pull requests. Scan dependencies. Audit rich text components. Review changes to templates and client-side rendering logic.
Logging and monitoring also matter. Suspicious input patterns, repeated rendering failures, abnormal redirects, and security header violations can provide early warning signs. Even if a defense catches an issue, that event is useful intelligence. It tells you where your application is being probed and where your guardrails matter most.
Finally, train the team. Developers, QA engineers, content managers, and product owners all influence this risk. The more people understand how injection happens, the less likely it is that someone will accidentally reintroduce an old bug in a shiny new feature.
Common Mistakes That Make JavaScript Injection Easier
- Assuming server-side validation alone solves the problem.
- Rendering raw HTML because it is faster than designing a safer content format.
- Using framework escape hatches without a security review.
- Forgetting that third-party content is untrusted content.
- Allowing rich text editors to process pasted or embedded content without strict rules.
- Using a weak CSP and calling it a day.
- Ignoring dependency updates for packages that parse HTML or templates.
A Practical Example
Imagine a support portal where customers can submit tickets and agents can view them in an internal dashboard. A team wants to make messages look nicer, so it allows basic formatting. That seems reasonable. But if the submitted content is not sanitized properly, and the dashboard renders it as active HTML, the agent’s browser becomes the real target.
A safer design is straightforward: validate the input format, sanitize allowed HTML with a strict policy, encode output for the specific rendering context, avoid risky client-side rendering shortcuts, and back it up with a strict CSP. The user still gets formatting. The team still gets functionality. The browser does not get tricked into executing something it never should have trusted.
Experience-Based Lessons From Teams That Deal With This Problem
One of the most common lessons teams learn is that JavaScript injection is rarely caused by a single outrageous mistake. More often, it is the result of several small decisions that look harmless in isolation. A product manager asks for custom formatting. A developer adds a shortcut to render content quickly. A reviewer assumes the sanitizer is stronger than it is. A third-party widget gets added during a deadline sprint. Then six months later, everyone is staring at the same page asking, “Who approved this?” The honest answer is usually, “All of us, a little.”
Teams that improve fastest are the ones that stop treating security as a dramatic last-minute event. They build predictable habits. They define safe rendering standards. They ban certain patterns unless there is a documented exception. They make code reviews specific enough to catch risky DOM operations. They test rich text features with the same seriousness they test payment flows. Once those habits are in place, security gets less theatrical and more boringin the best possible way.
Another big lesson is that developers appreciate clear rules more than vague warnings. “Be careful with user input” sounds wise, but it is not actionable. “Use escaped output by default, sanitize only approved HTML, do not bypass rendering protections, and route risky content through reviewed utilities” is much more useful. Good security guidance should reduce guesswork. If people need a detective novel to decide whether a rendering pattern is safe, the process is already too messy.
Experienced teams also learn that education works better when it includes examples tied to real features. A random lecture about XSS may be forgotten by next Tuesday. A short review of how a comment box, admin panel, or profile editor could create a browser-side risk tends to stick. It becomes memorable because it feels relevant. Engineers are far more likely to follow secure practices when they understand the exact part of the product that could break.
There is also a human lesson here: convenience is persuasive. When deadlines are tight, unsafe shortcuts can look awfully charming. Raw HTML rendering may feel like the hero of the sprint. But production has a cruel sense of humor. The shortcut that saved thirty minutes in development can create thirty days of cleanup later. Teams that have lived through that once usually become much more disciplined the second time around.
Finally, the most mature organizations do not celebrate “never having had an incident” as proof they are secure. They focus on whether their systems are resilient, observable, and easy to review. That mindset matters. Security is not about pretending bad things never happen. It is about making dangerous outcomes less likely, easier to detect, and harder to repeat. In practice, that means better defaults, stronger review culture, smarter tooling, and fewer opportunities for text to become code by accident.
Conclusion
Preventing JavaScript injection is not about panic. It is about discipline. If you identify input sources, validate aggressively, encode output for the right context, sanitize only when needed, avoid dangerous DOM patterns, add CSP and Trusted Types, control third-party code, and keep testing, you dramatically reduce the odds of turning a normal feature into a browser-executed security problem.
The smartest teams are not the ones who assume they will never face injection risk. They are the ones who build software as if the browser will faithfully execute anything confusing enough to slip through. Because, unfortunately, it often will. The browser is obedient. Your job is to make sure it has good instructions.